5 Solutions to Prevent Visual Hacking in Business Travel


Visual hacking, also known as "shoulder surfing," is the act of spying on someone else's private data by directly looking over their shoulder or using technology to view their display screen. Visual hacking in business travel is a growing threat for business travelers, especially when working on confidential information in public places like airports, hotels, coffee shops, and other open spaces.
With the rise of mobile technology and remote work, business travelers routinely access sensitive information in vulnerable environments where malicious actors may lurk. Through visual observation, cybercriminals can easily capture login credentials, intellectual property, trade secrets, financial data, and other proprietary information.
This article will explore five key solutions you can employ to prevent visual hacking in business travel and safeguard sensitive data in insecure environments.
1. Use Privacy Filters
Privacy filters, also known as privacy screens or shields, are one of the best solutions to visual hacking. They work by blocking the screen's visibility at wide viewing angles. They use optical films or micro louvers to direct light straight back to the user and obscure visibility from the sides. This makes it nearly impossible for strangers to sneak a peek at your screen since the content appears obscured or blank when viewed at an angle.
Attach privacy filters directly onto laptop screens or mobile devices to prevent visual hacking in business travel. Leading brands of privacy filters include 3M, Izatt, and Zagg. Look for filters that clip directly onto the screen or adhere using static cling without any adhesive that leaves residue. Some types also work through an electromagnetic charge built into the screen.
Make sure to get a filter sized correctly for your device's display. Using privacy filters, road warriors can safely work on confidential documents, financial data, client details, and more without worrying about prying eyes. They provide an easy and effective safeguard for visual hacking when traveling.
2. Encrypt Devices
It's vital to encrypt devices used for business travel, like laptops, tablets, and smartphones, to prevent data breaches. There are two main encryption options to implement:
Full disk encryption: This protects all of the contents of a device by scrambling data using encryption algorithms and an encryption key. Some popular full disk encryption tools include BitLocker for Windows and FileVault for Mac. Full disk encryption ensures no files can be accessed if the device is lost or stolen.
Encrypt sensitive files: Companies can also encrypt individual files containing sensitive corporate data for extra protection. This adds another layer of security so that even if full disk encryption is bypassed, sensitive files remain encrypted.
Encryption ensures that even if someone catches a glimpse of data, it will remain securely scrambled and inaccessible. Companies should mandate device encryption and provide access to approved encryption tools to maximize data security for traveling employees.
3. Limit Information Sharing
When traveling for business, it's important to limit the sensitive information that could be exposed in public settings. Visual hacking in business travel becomes easier for bad actors when confidential data is openly handled.
- Avoid accessing sensitive data like customer records, financial reports, or proprietary documents in public spaces like airports, hotels, restaurants, etc. Only access what is necessary and avoid exposing your screen.
- Be careful when plugging devices into public USB ports at airports, hotels, cafes, etc. Malware can be installed through public USB connections to steal data. Use a USB data blocker, or avoid plugging into public ports altogether.
- Turn device screens away from public view and enable screen privacy filters to obscure content.
- Avoid openly discussing confidential company information in public spaces where conversations can be easily overheard. Save those discussions for secure, private settings.
- Only connect to trusted, secure Wi-Fi networks and use a VPN for protection when accessing company data. Public Wi-Fi poses risks for visual hacking.
Business travelers can reduce risks associated with visual hacking attacks by limiting the sensitive information accessed and restricting device use in public. Handling confidential data with care goes a long way in preventing data breaches.
4. Use Password Protection
Protecting devices and accounts with strong passwords is one of the good solutions to visual hacking. Here are some tips:
- Set the device to auto-lock with a password or biometrics like fingerprint or facial recognition. This ensures that even if you leave your device unattended, prying eyes can't access your data. Require a password or biometric scan each time the screen locks or the device wakes from sleep mode.
- Use a password manager to generate and store strong, unique passwords. Password managers like LastPass make creating complex passwords easy and filling them in automatically. Never reuse passwords across accounts.
- Enable two-factor authentication on important accounts whenever possible. This adds an extra layer of protection beyond just a password.
- Avoid using obvious passwords like "password123" or personal info. Use passwords with 12+ random characters, numbers, symbols, and uppercase and lowercase letters.
- Change passwords regularly, at least every 90 days, for sensitive accounts. Don't use slight variations of old passwords.
- Never share passwords or write them down where others may access them.
Strong password hygiene limits the payoff for visual hackers even if they catch a peek at your screen or devices. Protect accounts and data by taking password security seriously.
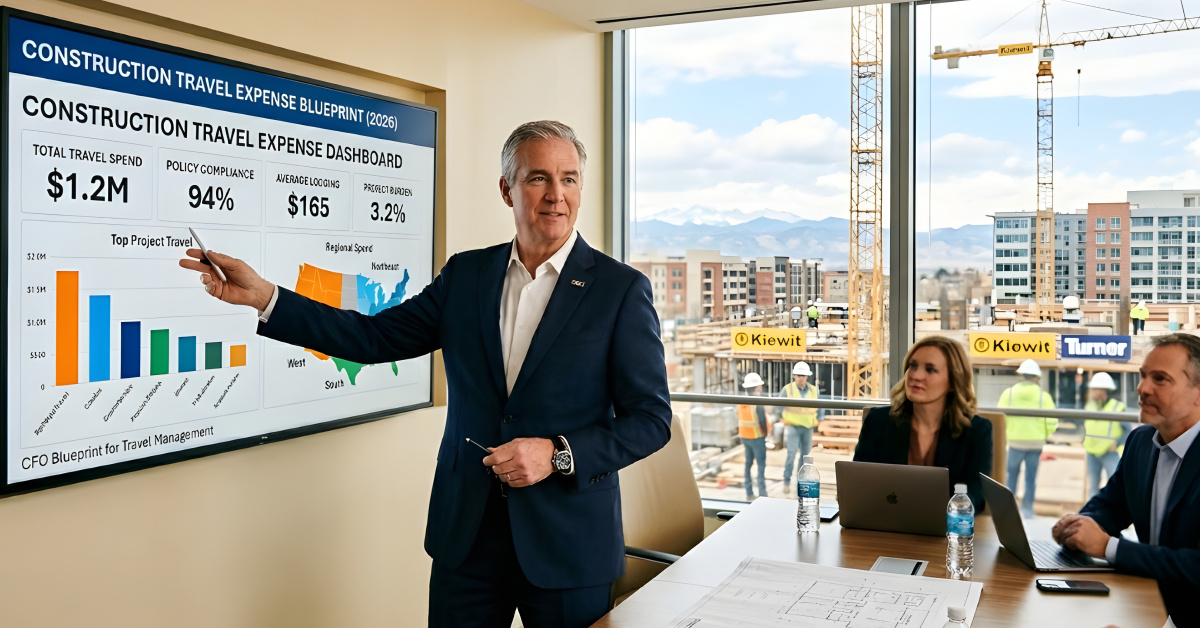
5. Leverage Travel Management Platforms
Travel management software provides features that can help protect business travelers from visual hacking. These platforms allow companies to remotely wipe stolen devices, ensuring sensitive data does not fall into the wrong hands.
They also enable encrypted chats between travelers and travel managers. This allows them to communicate securely regarding travel details, business travel expenses, and other confidential information. The chat history is not stored on the device, so past conversations remain protected even if compromised.
Some platforms even facilitate device locking to restrict unauthorized access. For example, a device idle for a set period will automatically lock until the approved user logs in.
By leveraging these travel management solutions, companies can enhance data and visual security for mobile and remote employees. The tools provide travelers with a secure digital environment that minimizes the risks associated with visual hacking in business travel and data theft on the road.
Ensure Data Safety With ITILITE
The above solutions to visual hacking can help you secure your date. With ITILITE, safeguarding your travelers' data is paramount and effortless. The software offers a secure and centralized repository where all pertinent traveler information is stored and managed.
ITILITE ensures that sensitive data remains encrypted and protected with robust security measures, from personal details and preferences to travel itineraries and booking records.
The platform enhances convenience and minimizes the risk of information loss or unauthorized access. Additionally, ITILITE’s compliance with industry-standard security protocols guarantees that your travelers' data is shielded against potential threats, ensuring peace of mind for your team and travelers throughout their journey.
Control Costs, streamline travel with 24/7 support.
A fully integrated corporate travel management software that dramatically reduces spends while improving user experience






.jpeg)


.jpeg)
.jpeg)

.webp)

.jpeg)
.jpeg)

.webp)







.png)