SaaS Security in the Travel Industry: Safeguarding Customer Data


In the travel industry, the handling of sensitive customer data is both a fundamental necessity and a significant responsibility. Travel service providers routinely collect and process a variety of personal and financial information, making it essential to understand the types of business travel data involved and their importance in delivering a seamless and secure travel experience.
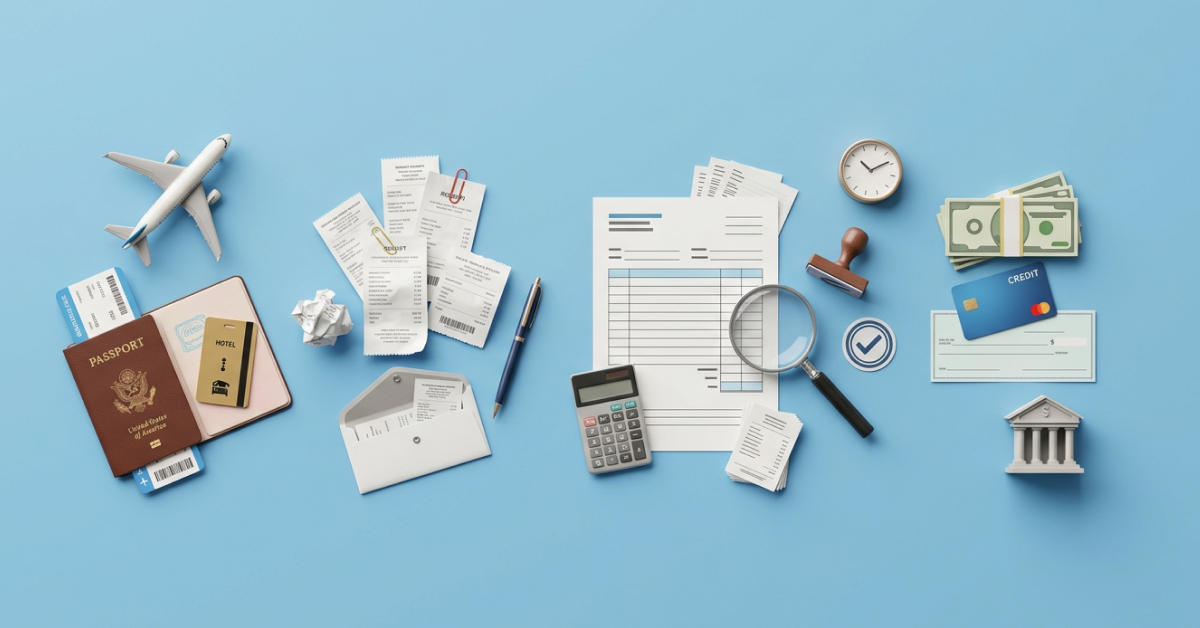
Types of Sensitive Customer Data in Travel
Personal Information
This includes things like your name, address, email, and phone number. It's used to set up and manage your travel plans, like booking flights and hotels. SaaS providers use this to make your experience more personal and to keep in touch with you.
Payment Details
When you buy airline tickets, book hotels, or rent cars, you use payment details like credit card numbers, bank account info, and billing addresses. Safeguarding this data is critical to avoid financial scams and identity theft.
Passport Information
If you're traveling internationally, passport details like the passport number, expiration date, and nationality are a must. They're needed for booking international flights and following immigration and customs rules. As a result, data security for international travel is even more crucial.
Travel Itineraries
Travel itineraries contain details of a customer's entire trip, including flight schedules, hotel reservations, car rentals, and activity bookings. SaaS providers use this information to offer customers a seamless travel experience and make arrangements on their behalf.
Consequences of Data Breaches
Data breaches in the travel industry can have severe consequences for both customers and SaaS providers:
1. Financial Loss for Customers
In the event of a data breach, customers can suffer financial losses due to fraudulent activities, such as unauthorized credit card charges and identity theft. It can take a significant amount of time and effort to resolve these issues, causing stress and inconvenience.
2. Damage to Customer Trust
Data breaches erode trust in SaaS providers. Customers rely on these companies to safeguard their sensitive information, and a breach indicates a failure to meet this expectation. As a result, customers may choose to take their business elsewhere, damaging the reputation and revenue of the SaaS provider.
3. Legal and Regulatory Consequences
Data breaches may result in legal consequences for SaaS providers. Depending on their location and the data involved, they may be subject to fines and penalties under data protection laws like GDPR and CCPA. Additionally, they might face lawsuits from affected customers seeking compensation for damages.
4. Reputational Damage
The reputation of a SaaS provider can be severely tarnished by a data breach. Customers and the broader public may lose faith in the company's ability to protect sensitive data. It can take years to rebuild a damaged reputation.
5. Operational Disruption
A data breach can lead to operational disruptions as the SaaS provider must investigate, contain, and remediate the breach. This diverts resources and attention away from providing quality services to customers.
6. Cost of Recovery
SaaS providers must invest significant resources in investigating the breach, notifying affected customers, offering credit monitoring services, and implementing security improvements. These costs can be substantial and ongoing.
Business Travel Data Security Threats
SaaS providers in the travel industry face a range of common security threats that can compromise the confidentiality, integrity, and availability of sensitive customer data.
Data Breaches: Data breaches occur when someone gains unauthorized access to your personal information, often because of security weaknesses, mistakes in settings, or even someone you trust turning against you.
Hacking and Cyberattacks: Cybercriminals try to get into your computer systems or services without permission. They might do this by finding software problems or by overloading your systems to make them crash.
Phishing Attacks: Phishing attacks involve tricking individuals into revealing sensitive information. Attackers send you fake emails or create fake websites to trick you into revealing your personal information, like passwords or credit card numbers.
Malware and Ransomware: Malware is a virus on your computer that can steal your data or even lock you out of your own files until you pay a ransom.
Insider Threats: Sometimes, people you trust, like employees or partners, may accidentally or intentionally harm your business travel data security by not following the rules or doing things they shouldn't.
Third-Party Vendor Risks: When you use services from other companies, they might not always be as secure as you'd like. If they have a security problem, it can indirectly affect you and your data.
Unsecured APIs and Integration Points: Think of APIs (Application Programming Interfaces) as doors that allow different computer systems to connect with each other. Ensuring the data security for travelers of these connections is vital to prevent data breaches.
Social Engineering Attacks: Some attackers manipulate your feelings to trick you into sharing sensitive information. They might pretend to be someone you trust, like customer support, and ask you for your personal data.
Data Interception and Eavesdropping: Hackers can intercept your online communication when it's not properly protected. This means they can listen in on your conversations and steal your information.
Credential Stuffing: If you use the same passwords for different accounts, hackers can use stolen login details to access multiple accounts you own. Always use strong, unique passwords to protect yourself from this threat.
Strategies for Safeguarding Customer Data
In the travel industry, safeguarding customer data is a top priority for SaaS providers. To achieve this, it's essential to implement robust business travel data security measures. Here, we explore best practices and strategies for enhancing SaaS security in the travel sector
1. Encryption
Data Encryption: Encrypt all sensitive customer data both in transit and at rest. Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols can be used for securing data in transit, while encryption algorithms like AES can protect data at rest. Encryption ensures that even if a breach occurs, the data remains unreadable to unauthorized parties.
2. Access Controls
Role-Based Access Control (RBAC): Implement RBAC to limit access to customer data. Assign permissions and privileges based on job roles, ensuring that only authorized personnel can access specific information.
Multi-Factor Authentication (MFA): Enforce MFA for system logins to add an extra layer of security. This requires users to provide more than one piece of evidence to verify their identity.
Audit and Monitor Access: Regularly monitor access to sensitive data and set up alerts for any suspicious activity. Audit logs help in tracing unauthorized access or changes to the system.
3. Employee Training
Security Awareness Training: Train employees to recognize and respond to security threats like phishing attacks and social engineering. Ensure that they are aware of best practices and can contribute to the organization's security culture.
Data Handling Procedures: Educate employees on how to handle sensitive data, emphasizing the importance of secure password management and not sharing sensitive information.
4. Intrusion Detection and Prevention Systems (IDPS)
Continuous Monitoring: Implement IDPS to monitor network and system activity in real time. This system can detect and respond to suspicious activities and potential business travel data security breaches.
Automated Responses: Configure IDPS to take automatic actions when a threat is detected, such as blocking IP addresses or isolating compromised systems to prevent further damage.
Regular Updates: Keep IDPS updated with the latest threat intelligence to stay ahead of emerging security risks.
5. Regular Security Audits and Penetration Testing
Conduct regular business travel data security audits and penetration testing to identify vulnerabilities in your systems and applications. This proactive approach helps you find weaknesses before malicious actors can exploit them.
6. Data Backups and Disaster Recovery Plans
Regularly back up customer data and develop a robust disaster recovery plan. This ensures that even if a data breach occurs, you can quickly restore operations and customer data to minimize downtime.
7. Vendor Due Diligence
Evaluate the data security for travelers practices of third-party vendors, especially those providing critical services. Ensure that they meet your security standards and comply with relevant regulations.
8. Incident Response Plan
Develop a comprehensive incident response plan outlining steps to take in case of a data breach. This plan should include communication protocols, responsibilities, and legal requirements for reporting breaches to authorities and affected customers.
9. Compliance with Data Protection Regulations
Ensure compliance with relevant data protection regulations like GDPR or CCPA. This includes obtaining necessary consent, providing data access to customers upon request, and reporting breaches as required by law.
Trust Itilite for Business Travel Data Security
At itilite, we're not just about managing travel; we're dedicated to ensuring your data's privacy and security so you can travel with peace of mind. Our commitment to global regulations and industry best practices is unwavering, guaranteeing that your information is safeguarded at every step of your journey.
Global Compliance
Itilite is your GDPR-ready companion, helping you effortlessly meet your compliance obligations. We've got you covered so you can focus on what matters most – your travel.
Role-Based Access
We believe in the principle of least privilege, ensuring that only those who absolutely need access get it. We add an extra layer of security with two-factor authentication while our end-to-end audit trails keep a vigilant eye on every access point.
Bulletproof Encryption
Your data is our treasure, and we guard it with AES 256-bit encryption boasting 1,024-bit key strength. Our FIPS 140-2 compliant TLS encryption keeps your data safe during transit.
Disaster Recovery
We don't leave anything to chance. Our Disaster Recovery program ensures that our services remain resilient and readily available, even in the face of a disaster. We've built a robust technical environment and disaster recovery plans, regularly tested to perfection.
Unleash the power of itilite and travel smarter, safer, and more efficiently.
Control Costs, streamline travel with 24/7 support.
A fully integrated corporate travel management software that dramatically reduces spends while improving user experience


.png)


.jpeg)


.jpeg)
.jpeg)

.webp)

.jpeg)
.jpeg)

.webp)